My Last Email with W. Richard Stevens
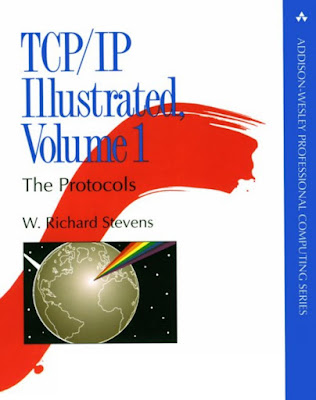
In the fall of 1998 I joined the AFCERT. I became acquainted with the amazing book TCP/IP Illustrated, Volume 1: The Protocols by W. Richard Stevens. About a year later I exchanged emails with Mr. Stevens. Here is the last exchange, as forwarded from my AFCERT email address to my home email. From "Capt Richard Bejtlich - Real Time Chief" Mon Sep 6 18:27:35 1999 X-Mozilla-Keys: Received: from kinda.csap.af.mil (kinda.csap.af.mil [192.203.2.250]) by mw4.texas.net (2.4/2.4) with SMTP id RAA22116 for <bejtlich@texas.net>; Mon, 6 Sep 1999 17:27:38 -0500 (CDT) Received: by kinda.csap.af.mil (Smail3.1.29.1 #7) id m11O7Ee-000NcwC; Mon, 6 Sep 99 17:27 CDT Received: from walt.ip.af.mil(192.168.1.142) by kinda via smap (V1.3) id sma014865; Mon Sep 6 17:27:36 1999 Received: from kinda.csap.af.mil by walt.ip.af.mil with smtp (Smail3.1.29.1 #6) id m11O7Ed-000VruC; Mon, 6 Sep 99 2